AiTM/ MFA phishing attacks in combination with new Microsoft protections (2023 edition)
Por um escritor misterioso
Descrição
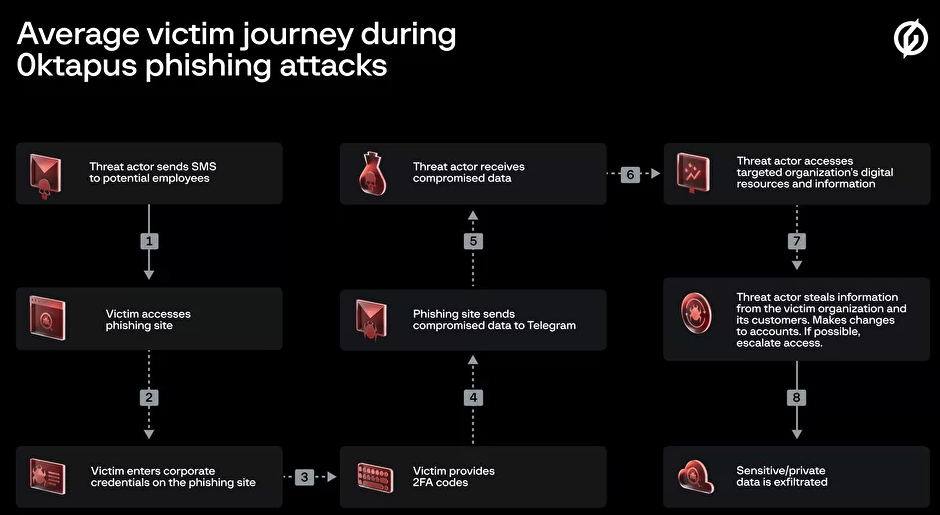
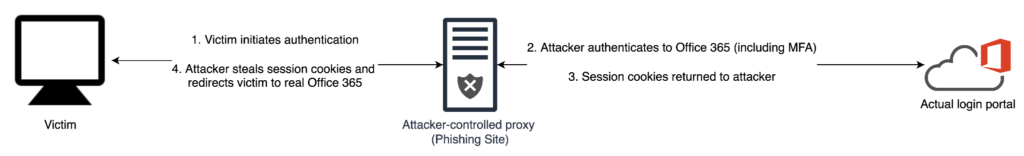
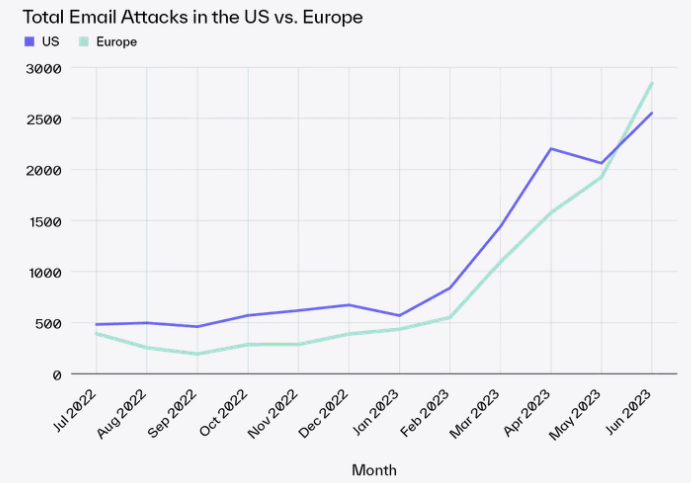
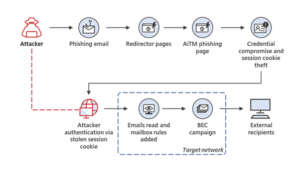
Adversary-in-the-middle phishing attacks are still more common in use. Since the removal of basic authentication from Exchange Online more and more attackers are using more modern attacks like adversary-in-the-middle phishing, cookie theft, and other used attacks. Last year I blogged about several modern
How 1-Time Passcodes Became a Corporate Liability – Krebs on Security
Netskope Threat Coverage: Microsoft Discloses New Adversary-in-the-Middle ( AiTM) Phishing Attack - Netskope
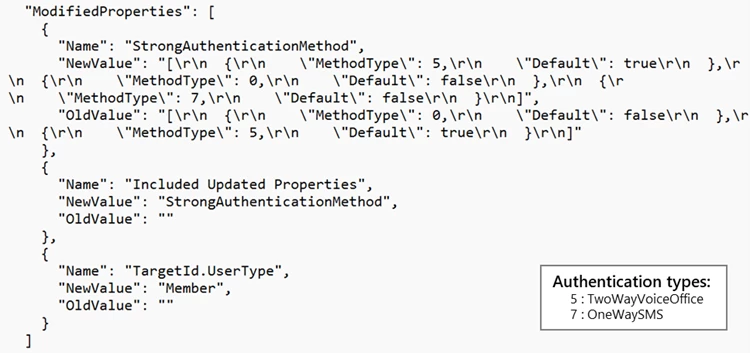
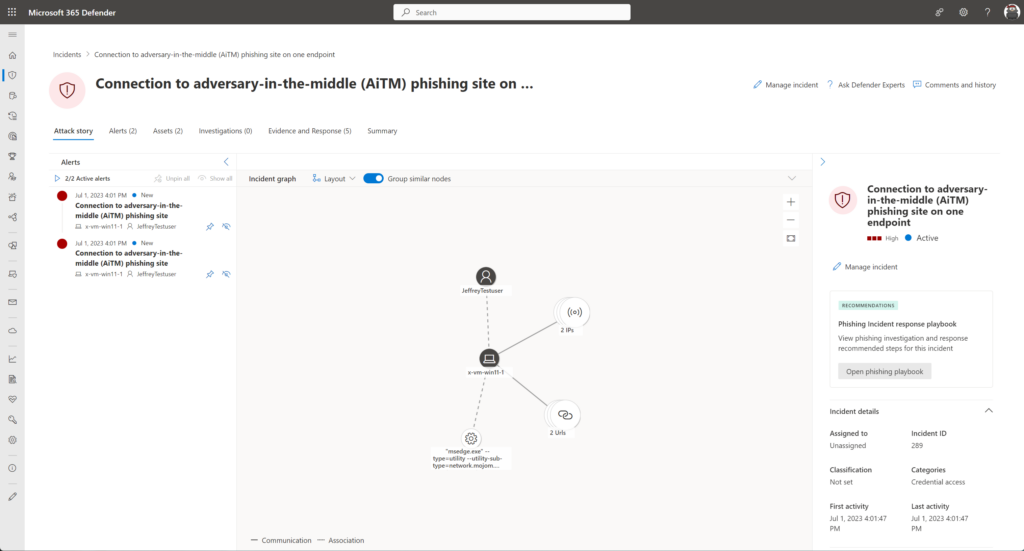
Detecting and mitigating a multi-stage AiTM phishing and BEC campaign

Protecting Enterprises Against Phishing and Business Email Compromise (BEC) Attacks - Spiceworks
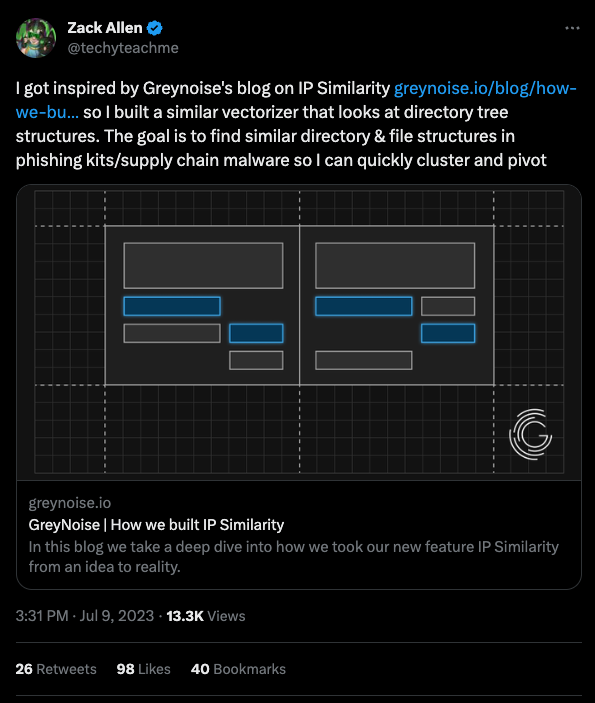
Detection Engineering Weekly #31 - MOVEit, get out the way
How to protect against BEC & AiTM attacks via Microsoft 365 Defender, Automatic Attack Disruption, by Derk van der Woude
Rising AiTM phishing attacks: how to protect against them

Jeffrey Appel on LinkedIn: How to protect Azure storage accounts (Blob) using Defender for Storage

Preventing Cloud Identity Compromise – CraigCloudITPro

What Is An Adversary-in-The-Middle Attack (AiTM)?
AiTM/ MFA phishing attacks in combination with new Microsoft protections (2023 edition)

What is an Adversary-In-The-Middle (AiTM) Phishing Attack? - 1Kosmos
de
por adulto (o preço varia de acordo com o tamanho do grupo)


.jpg)


