SILKLOADER: How Hackers Evade Detection
Por um escritor misterioso
Descrição
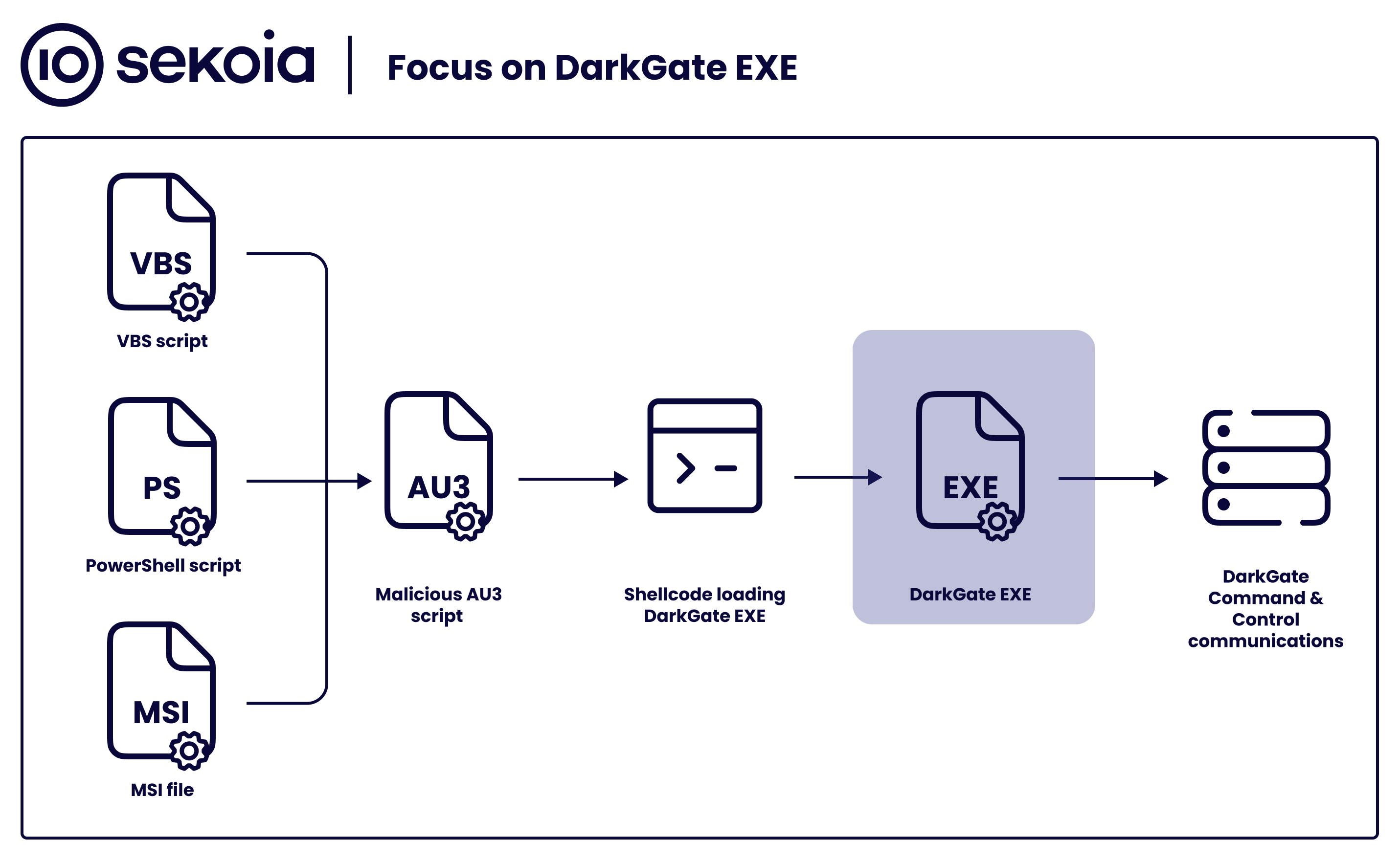
As the cyber threat landscape continues to evolve, hackers are employing increasingly sophisticated techniques to evade detection. One such example is the SILKLOADER malware, which has recently gained attention for its stealth capabilities.

Types of Evasion Technique For IDS - GeeksforGeeks

Chinese Hackers Use New Cryptojacking Tactics to Evade Detection

Hackers Using Golang Variant of Cobalt Strike to Target Apple macOS Systems
Lynx-CERT

Robert E. on LinkedIn: Chinese and Russian Hackers Using SILKLOADER Malware to Evade Detection
Windows Red Team Defense Evasion Techniques - HackerSploit Blog

MALWARE DETECTION : EVASION TECHNIQUES - CYFIRMA

Black Arrow Cyber Consulting — Black Arrow Cyber Threat Briefing 17 March 2023

SILKLOADER: How Hackers Evade Detection

New Godlua Backdoor Found Abusing DNS Over HTTPS (DoH) Protocol - Noticias de seguridad - Trend Micro ES
de
por adulto (o preço varia de acordo com o tamanho do grupo)